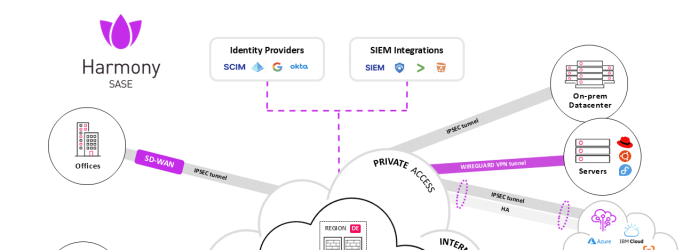
As organizations embrace cloud computing, remote work, SaaS applications, and distributed teams, traditional perimeter-based security models are no longer effective. Backhauling traffic through a central data center introduces latency,...
Below is the cheatsheet for network admins for subnet masks: / Addresses Hosts Netmask Amount of a Class C...
Before diving into the differences between these two, we need to understand that what penetration testing (aka pen-testing) is....